You are seeing a free-to-access but limited selection of the activity Altmetric has collected about this research output.
Click here to find out more.
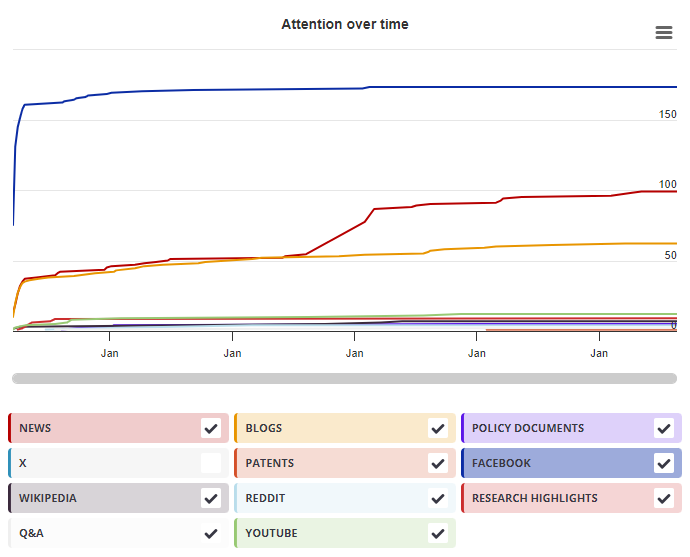
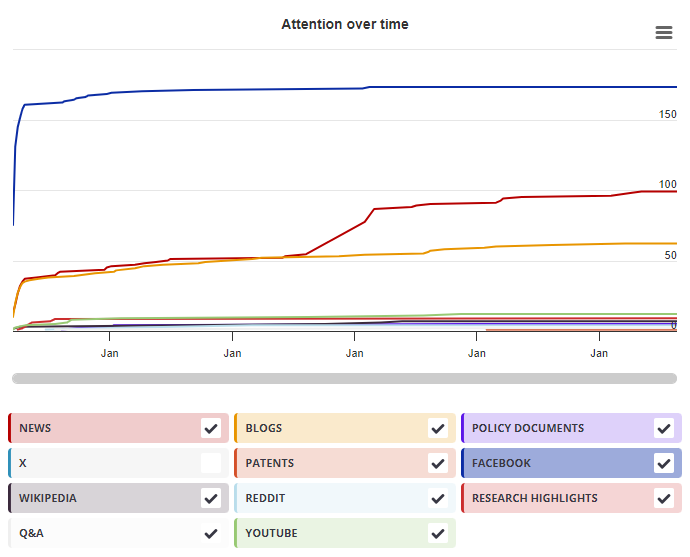
Timeline
Mendeley readers
| Chapter title |
Revisiting MAC Forgeries, Weak Keys and Provable Security of Galois/Counter Mode of Operation
|
|---|---|
| Chapter number | 2 |
| Book title |
Cryptology and Network Security
|
| Published by |
Springer, Cham, November 2013
|
| DOI | 10.1007/978-3-319-02937-5_2 |
| Book ISBNs |
978-3-31-902936-8, 978-3-31-902937-5
|
| Authors |
Bo Zhu, Yin Tan, Guang Gong, Zhu, Bo, Tan, Yin, Gong, Guang |
Mendeley readers
The data shown below were compiled from readership statistics for 21 Mendeley readers of this research output. Click here to see the associated Mendeley record.
Geographical breakdown
| Country | Count | As % |
|---|---|---|
| Unknown | 21 | 100% |
Demographic breakdown
| Readers by professional status | Count | As % |
|---|---|---|
| Student > Ph. D. Student | 9 | 43% |
| Researcher | 3 | 14% |
| Student > Master | 2 | 10% |
| Lecturer | 1 | 5% |
| Professor | 1 | 5% |
| Other | 3 | 14% |
| Unknown | 2 | 10% |
| Readers by discipline | Count | As % |
|---|---|---|
| Computer Science | 18 | 86% |
| Physics and Astronomy | 1 | 5% |
| Unknown | 2 | 10% |
